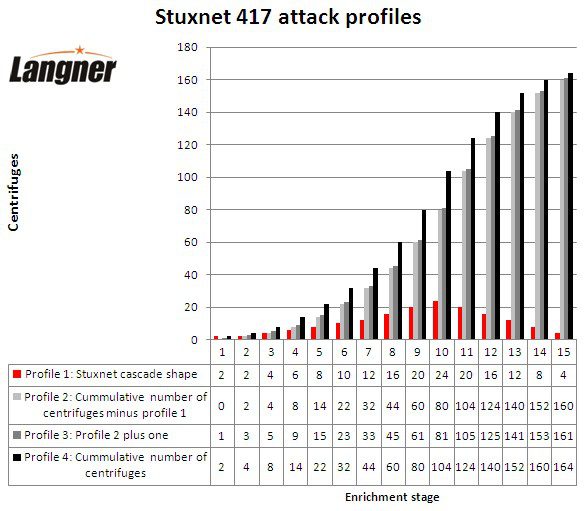
When you think long enough about the cascade shape and have all the numerical values available, it gets easy to determine how the attack profiles mentioned earlier are constructed. Profile one is simply the cascade shape. Profile four is the cumulative number of centrifuges from the shape. Profile two is the delta, it computes by subtracting profile one from profile four. Profile three is profile two plus one. So after all, they’re not profiles in the sense that they would be processed sequentially stage by stage. They appear to be more like patterns that are associated with the individual enrichment stages.