OT Security Blog Articles
Insights on Resilience, Vulnerability Management, and More
Thinking outside of the box: Mastering OT security is not about defending against threats
Fact is that oftentimes the chances that an asset owner’s investment in ICS Detection technology and related services easily exceeds the damage that could reasonably be expected from a cyber-physical attack.
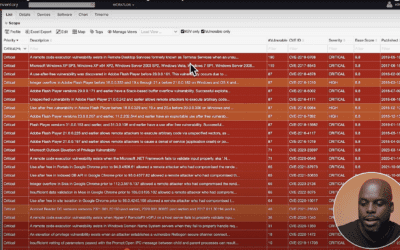
Mastering CVE Matching for OT assets
In the world of Operational Technology (OT), we find several orders of magnitudes more vulnerabilities than in IT. Therefore, vulnerability identification and management becomes a much more challenging task that requires a dedicated tool. Vulnerability matching is one...
Maintaining OT Resilience: Balancing Security and Engineering Needs
Several other engineering use cases are just as important, if not more so. In this blog post, we’ll explore some of the engineering use cases OTbase addresses and explain why they’re just as crucial as managing common security use cases.
Why Engineers Need to Move Away from Excel: The Case for Automated Discovery and Inventory of OT Assets
Automated inventory solutions can provide real-time visibility, accuracy, scalability, and compliance, which are essential for modern OT environments’ complex requirements. By automating the inventory process, engineers can free up time to focus on other critical tasks, improve accuracy, and reduce the risk of security incidents.
Understanding The Basics of OT asset management
By following these basic principles, organizations can effectively manage their operational technology assets, ensure their reliability and security, and optimize the performance of their industrial processes.
Mastering OT Vulnerability Management: Simplifying the Process with Automation
A single vulnerability can cause substantial damage to critical infrastructure and result in significant security breaches. However, managing OT vulnerabilities is not always a simple process. It can be intimidating, especially when performed manually. Therefore, OT vulnerability management must be automated to increase efficiency and effectiveness.
5 Reasons Why Effective OT Security Requires An Accurate Asset Inventory
In the current digital era, the manufacturing and oil and gas industries extensively rely on technology to increase efficiency and productivity. However, as technological dependence increases, so does the risk of cyber attacks and security breaches. For the success of these industries, an effective operational technology (OT) asset inventory is essential.
Why Passive Scanning Won’t Cut It: Oil and Gas Companies Need Active Probing
Oil and gas companies must use active probing as part of their OT strategy if they want to stay safe, reliable, and efficient. This will give us the visibility, speed, and accuracy we need to find threats and issues quickly, deal with them, and fix them before they become big problems.
What are Tangible Results in OT Security?
Fact is that oftentimes the chances that an asset owner’s investment in ICS Detection technology and related services easily exceeds the damage that could reasonably be expected from a cyber-physical attack.