OT Security Blog Articles
Insights on Resilience, Vulnerability Management, and More
What is OT/ICS configuration management, and how does it benefit engineers, admins, and auditors?
OT configuration management is the process of assuring consistency of OT system design with requirements. It helps you to gradually arrive at more robust network architectures, standardized software configurations, better maintainability, and higher security posture....
When will we see another Stuxnet & Nitro Zeus attack against Iran?
Eight years after we had uncovered that Stuxnet was a targeted cyber-physical attack against the Iranian nuclear program, both the United States and Israel find themselves threatened by the prospect of an Iranian breakout towards nuclear weapons production. This...
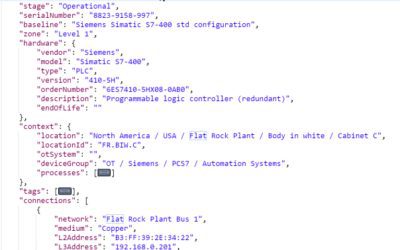
Importing OT/ICS Asset Data into your Enterprise Applications
Suppose you already have a great OT asset management system. It automatically discovers the identity and configuration of your PLCs, RTUs, network switches, operator stations and so forth. Your engineers use this system as their central hub for documenting the...
Understanding OT/ICS Asset Discovery: Passive Scanning vs. Selective Probing
For businesses large and small, digital operations technology has become a key driver of efficient production. But honestly, do you still exercise full control over your OT assets? If you are like most asset owners, you probably don't know exactly how many PLCs, RTUs,...
Misjudging OT security risk, part 2: Comparing cost/benefit
In a preceding blog article we discussed the logical flaw in network anomaly detection marketing collateral: Vendors emphatically advocate "passive scanning" with the argument that "active scanning" would be too dangerous, yet focus on completely different risks...
Misjudging OT security risk: The case of “active” vs. “passive” scanning
If you have followed the marketing buzz in the OT security software space, you cannot have missed the hype around "passive network scanning", which is a hallmark of network anomaly detection products. Interestingly, this buzz expects you to ignore the following...
Die fünf besten Schutzmaßnahmen gegen Cyber-Angriffe und Schadsoftware
Wer die Medien verfolgt, weiß: Ausgefeilte und umfangreiche Cyber-Angriffskampagnen nehmen zu. Das führt gemeinhin zu zwei unterschiedlichen Reaktionen. Einige Beobachter verfallen in Fatalismus, da gegen staatliche Angreifer aus Russland, China usw. wohl ohnehin kein...
Was steckt hinter dem Cyber-Angriff auf das Triconex-Safety-System?
Nun ist es also passiert: Erstmals wurde mit voller Absicht ein Safety-System in einer chemischen Anlage im Produktivbetrieb mit Schadsoftware angegriffen. Der Angriff wurde rechtzeitig erkannt, bevor Schaden angerichtet werden konnte. Kein Grund zur Entwarnung jedoch...
Siemens S7 als Proxy-Server für Cyber-Angriffe in das Prozessnetz
Dreizehn Jahre hat es gedauert, bis chinesische Hacker herausgefunden haben, wozu man die Step7-Kommunikationsbausteine TCON, TSEND und TRECV gebrauchen kann: Um eine S7 in einen Proxy-Server umzufunktionieren, von dem aus sich Cyber-Angriffe in das Prozessnetz...